While producing high-technology mobile apps and websites, there’s no way without security issues. That is why there are many top-notch pentest-tools for handling multiple workflows that allow detection and elimination, as well as prevention of any web security attacks.
What is Penetration Testing?
The idea behind any penetration testing is to identify security-related vulnerabilities in a software application by conducting a security attack to determine how much damage a hacker may cause when trying to hack the product. The results of this practice help to make applications and software more secure, robust, and unbreakable, and the users’ experience – more successful.
So, if you are going to develop and use any software for your business, the automated penetration testing method will help you to check network security threats.
How Penetration Tests Work
Penetration testing is a simulated real-time cyber-attack conducted by certified security professionals (hackers) under secure conditions to detect gaps, glitches, vulnerabilities, loopholes, misconfigurations, etc. that are susceptible to further malicious code injections, malware, unauthorized entries, attacks, etc.
Application testers then try and exploit these vulnerabilities, typically by stealing data, escalating privileges, intercepting traffic, etc., to understand the nature of damage they may cause. However, it’s hard to find all possible vulnerabilities using automated tools. There are some threats that can only be identified by manual system scans.
Types of Penetration Tests
To uncover the security vulnerabilities which can be found in any type or kind of Web Application, we may find three major tests types, which are as follows:
Check out the three following test types a bit in detail:
Black box testing
A black box assessment is mostly performed without any knowledge of the system’s internals. Here testers check out the system solely from the outside. They have no idea of what is happening within the system to generate responses and to test actions.
White box testing
In a white box assessment, the testers have the fullest and most complete internal knowledge of the system that’s being tested (design docs, source code, etc.).
Gray box testing
Gray box testing is another application security test technique that is a mix of both white box and black box testing.
Best Penetration Testing Software
Check out at least the following ten professional tools for holistic website pen testing worthy to exploit if you need a quality check of your app server response, attack proof or any other vulnerabilities.
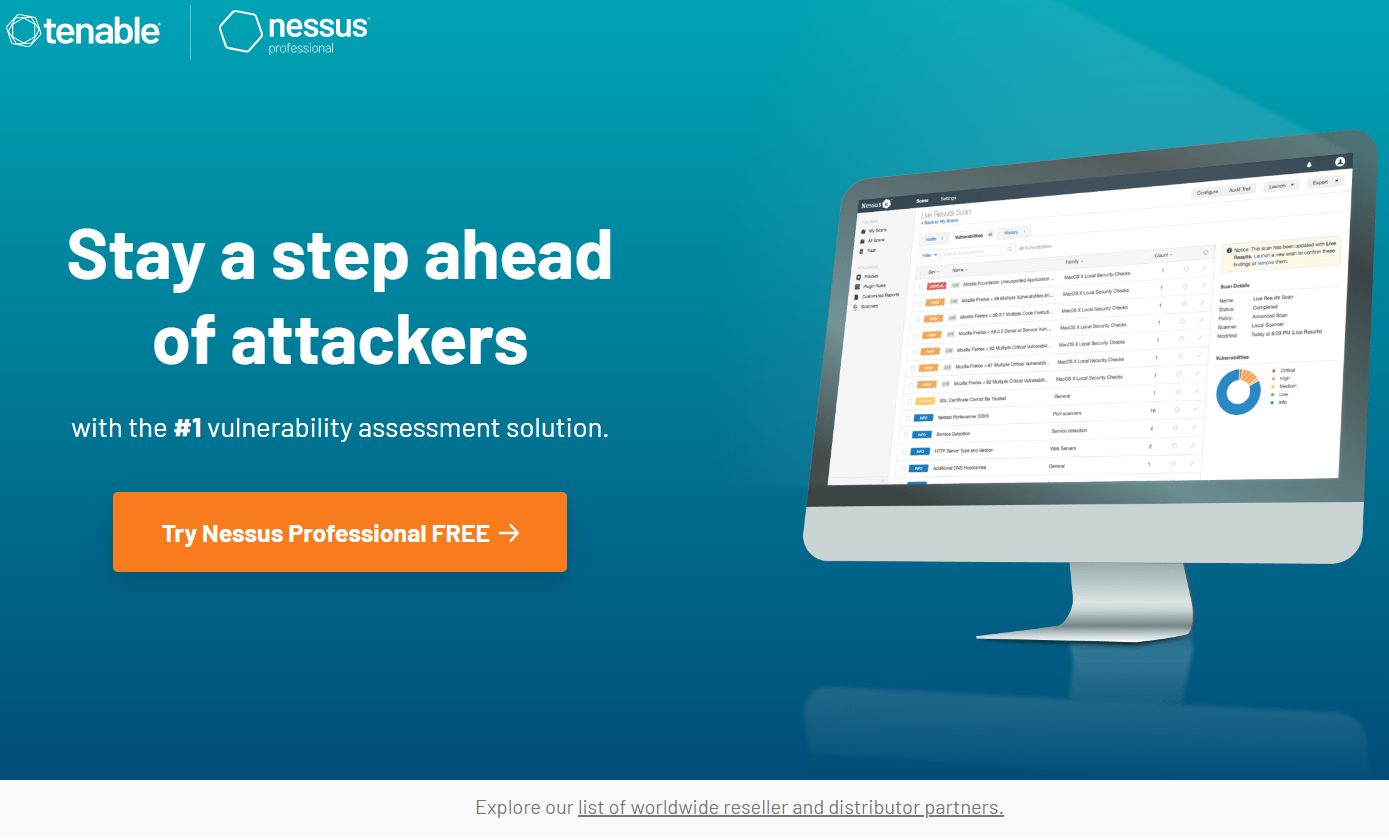
1. Nessus
Nessus is one of the most reliable and impressive threat detection scanners and penetration testing tools that specializes in finding sensitive data, checking compliance, scanning websites, etc. to find weaknesses. Compatible with multiple environments, this is one of the best tools out there.
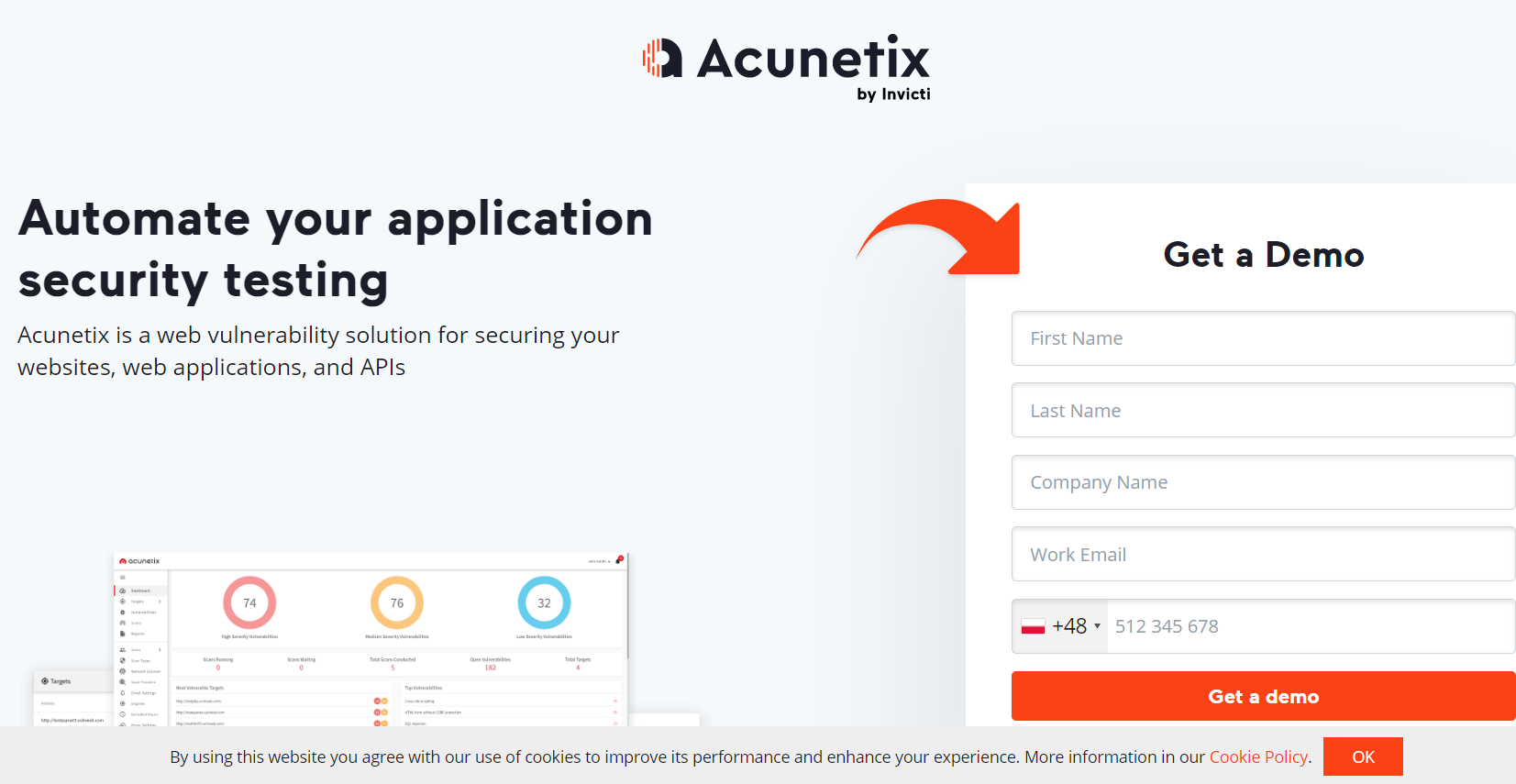
2. Acunetix
A fully automated web scanner, Acunetix checks for vulnerabilities by listing over 4500 web application threats that also include XSS and SQL injections. This tool works by automating tasks that can take hours to complete manually to provide the desired and consistent results.
3. Hackerone
This best security tool will help you find and fix the most important threats. This fast and efficient tool runs on a hacker-driven platform and instantly reports when any threat is detected. It opens up a channel allowing you to communicate directly with your team using tools like Slack, offering interaction with Jira and GitHub so you can communicate with development teams.
4. Invicti
Former Netsparker, Invicti is another automatic scanner available for Windows and an online service that detects threats related to cross-site scripting and SQL injection in web applications and APIs. This tool checks for vulnerabilities to prove they are real and not false positives, so you don’t have to spend a lot of time manually checking for vulnerabilities.
5. Metasploit
An advanced and sought-after penetration testing framework based on an exploit that includes code that can pass through security standards and infiltrate any system. When invading, it executes a payload to perform operations on the target machine to create an ideal basis for penetration testing.
6. Core Impact
Core Impact has an impressive exploit suite on the market that allows you to run free Metasploit exploits within the framework. With the ability to automate processes with wizards, they have an audit trail for PowerShells to retest clients by simply replaying the audit.
7. Intruder
Intruder offers the best and most effective way to find cybersecurity vulnerabilities while explaining the risks and helping you find remedies. This automate tool is designed for penetration testing and includes over 9000 security checks.
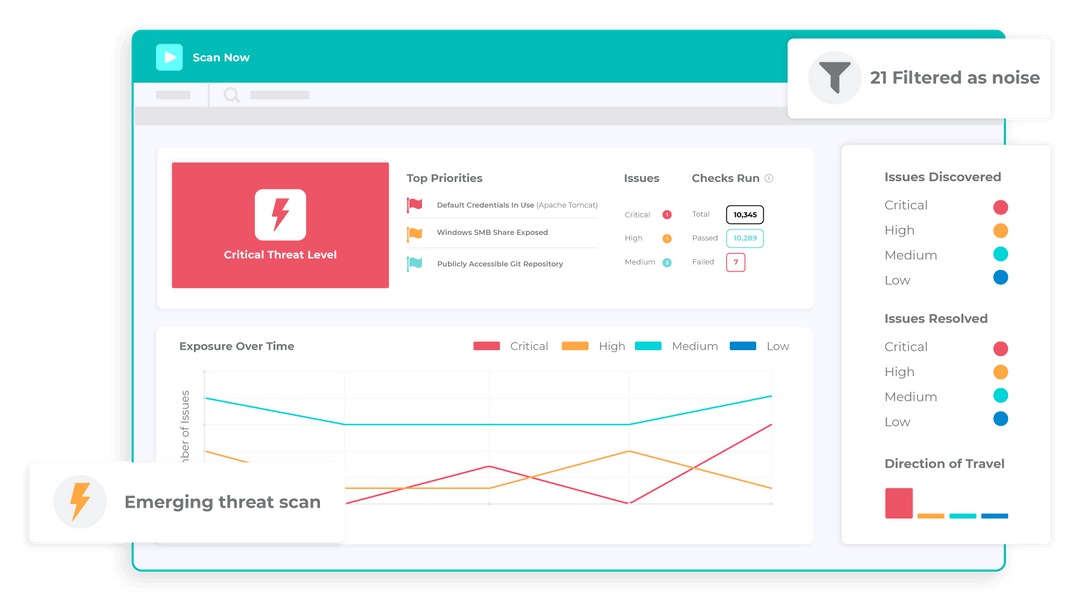
8. Breachlock
Breachlock or RATA (Reliable Attack Testing Automation) Web Application Threat Detection Scanner which is an automated scanner based on artificial intelligence or artificial intelligence, cloud and human hacking that requires special skills or experience or any hardware or software installation.
9. Wireshark
Wireshark is a popular network protocol analyzer that provides all the little details related to packet information, network protocol, decryption, etc. Suitable for Windows, Solaris, NetBSD, OS X, Linux, and more, it extracts data using Wireshark, which can be observed using the TShark utility in TTY mode or GUI.
10. Kali Linux
Having surpassed malicious network security, Kali Linux has become an open source Linux distribution that includes full customization of Kali ISOs, accessibility, full disk encryption, Live USB with multiple storages, Android compatibility, disk encryption on Raspberry Pi2 and much more.
Conclusion
Maintaining proper security while identifying real threats and damage that may be inflicted on your system by criminal hackers is the most essential in high-quality product development. Penetration testing software will be used in cases where traditional QA is not just enough to meet the security standards for your future mobile or web app, network, or any other product. To exploit any threat issues and eliminate them, always rely on professional cross-platform app development company and/or QA services company testers that apply deep knowledge with the top-notch automated penetration testing tools for checking out the most sophisticated products in no time.